A new security exploit was discovered that allows attackers to unlock any PC running Windows or Linux in less than five minutes via a Thunderbolt port. The vulnerability was found by Dutch researcher Björn Ruytenberg through a method aptly called Thunderspy, which can bypass the login screen of any PC.
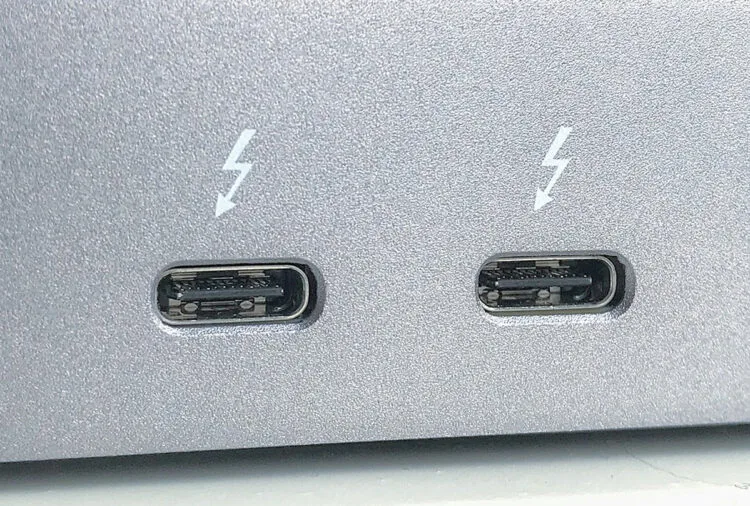
According to the researcher, this method of attack requires physical access to the device, therefore port connectivity such as Thunderbolt can be exploited for this breach. The primary reason why the port is effective is due to its fast protocol which partially allows direct access to a computer’s memory.

Ruytenberg added that there is actually a feature built into the Thunderbolt firmware called “Security Level”, which disallows access to untrusted devices and even turns off the port altogether. However, he explained that the Thunderspy approach is able to alter the firmware setting of the port’s control chip, thus allowing any device to access the PC without leaving any traces.
Fortunately, this vulnerability is something that everyday users shouldn’t be concerned with. Apart from requiring physical connectivity to fully exploit this security flaw, Ruytenberg said that this procedure will also require around US$400 (RM1,730) worth of hardware. So unless you’re a high value target, it’s very unlikely that someone would go through such lengths just to access your PC or laptop with this Thunderbolt vulnerability.
(Source: Thunderspy via TechPowerUp | Images: Wikimedia)